Welcome to the “Best 150 Computer General Knowledge Questions & Answers 2025” comprehensive guide! These days, artificial intelligence, cloud computing, and digital transformation shape our world. Knowing a lot about computers isn’t just helpful; it’s necessary for getting ahead in your job, doing well in school, and staying relevant in a tech-driven world.
This blog has been completely redesigned to represent the newest technological advances and the needs of the industry in the year 2025. You can find complete, correct, and useful answers here whether you’re a student studying for competitive exams like UPSC, bank exams, or tech certifications, a working professional wanting to advance in your career, a job candidate trying to stand out during the interview process, or just someone who is really interested in how modern technology affects our lives.
- What is Computer?
- Computer Fundamentals & Architecture
- Computer History & Generations
- Network & Internet Technology
- Cybersecurity & Data Protection
- Cloud Computing & Edge Computing
- Artificial Intelligence & Machine Learning
- Web3, Blockchain & Cryptocurrency
- DevOps, Docker & Kubernetes
- Data Science & Big Data
- Programming Languages & Software Development
- Emerging Technologies & Future Trends
- Conclusion
What is Computer?
A computer is a piece of electronics that can handle, store, and get information. It does many things by following the directions in different software programs. Computers are very flexible and can be used for many things, including talking to people, having fun, fixing problems, analyzing data, and more.
Computer Fundamentals & Architecture
Q1. What is the full form of CPU?
A. Central Processing Unit. It is the primary component that executes instructions from programs and performs all computational tasks.
Q2. Define RAM and its primary function.
A. RAM stands for Random Access Memory. It is volatile memory that temporarily stores data and programs currently being used by the CPU for fast access.
Q3. What is the difference between RAM and ROM?
A. RAM is volatile and loses data when power is turned off, while ROM (Read-Only Memory) is non-volatile and retains data permanently. ROM stores firmware or boot instructions.
Q4. What is an ALU in a CPU?
A. ALU (Arithmetic Logic Unit) is the component of the CPU that performs arithmetic operations (addition, subtraction, multiplication) and logical operations (AND, OR, NOT).
Q5. Explain the role of the Control Unit in a CPU.
A. The Control Unit manages instruction execution by fetching, decoding, and directing instructions to appropriate components of the CPU for processing.
Q6. What is the motherboard?
A. The motherboard is the main printed circuit board that connects all components of a computer (CPU, RAM, GPU, storage) through electrical pathways and buses.
Q7. Define a microprocessor.
A. A microprocessor is a computer processor where all CPU components (ALU, control unit, registers) are integrated on a single silicon chip (IC).
Q8. What is cache memory?
A. Cache memory is ultra-fast memory located directly on the CPU that stores frequently accessed data, reducing the need to fetch data from slower RAM.
Q9. What are the three types of cache memory?
A. L1 Cache (smallest, fastest, on-chip), L2 Cache (medium size, on-chip but separate), L3 Cache (larger, shared among cores).
Q10. Define a bit and byte.
A. A bit is the smallest unit of data (0 or 1). A byte consists of 8 bits and is the standard unit for data storage and measurement.
Q11. What is the difference between HDD and SSD?
A. HDD (Hard Disk Drive) uses magnetic spinning disks and is slower but cheaper. SSD (Solid State Drive) uses flash memory, offering faster speeds and better reliability.
Q12. What are input devices? Give examples.
A. Input devices allow users to communicate with computers. Examples: keyboard, mouse, scanner, microphone, webcam, joystick, touchscreen.
Q13. What are output devices? Give examples.
A. Output devices display or produce information from computers. Examples: monitor, printer, speaker, projector, headphones, smart display.
Q14. What is GPU (Graphics Processing Unit)?
A. GPU is a specialized processor designed for parallel processing of graphics and visual data, now also used for AI, machine learning, and scientific computing.
Q15. Define firmware.
A. Firmware is permanent, low-level software that controls hardware operations. BIOS (Basic Input/Output System) is a common example of firmware.
Q16. What is a bus in computer architecture?
A. A bus is a communication system that transfers data between CPU, RAM, and other components using parallel electrical pathways.
Q17. What is the Front Side Bus (FSB)?
A. FSB is the bus connecting the CPU to the motherboard and other components, determining the maximum data transfer rate between processor and system.
Q18. Define bandwidth in computer context.
A. Bandwidth refers to the maximum amount of data that can be transmitted over a communication channel or bus per unit time, typically measured in megabits (Mbps) or gigabits (Gbps).
Q19. What is clock speed and how is it measured?
A. Clock speed is the rate at which a CPU executes instructions, measured in Gigahertz (GHz). Higher clock speed generally means faster processing.
Q20. What is multi-core processing?
A. Multi-core processing uses multiple processors on a single chip, allowing simultaneous execution of different tasks, improving overall performance and efficiency.
Q21. Define overclocking.
A. Overclocking is the practice of increasing a CPU’s clock speed beyond manufacturer specifications to boost performance, though it increases heat and power consumption.
Q22. What is BIOS?
A. BIOS (Basic Input/Output System) is firmware that initializes and tests hardware components during computer startup before loading the operating system.
Q23. What is the POST process?
A. POST (Power-On Self-Test) is the diagnostic procedure BIOS performs when a computer starts up to verify hardware functionality.
Q24. Define Chipset.
A. A chipset is a group of integrated circuits on the motherboard that manages communication between the CPU, RAM, storage, and peripherals.
Q25. What are registers in CPU?
A. Registers are the fastest storage locations within the CPU that temporarily hold data being processed, instruction addresses, and control information.
Computer History & Generations
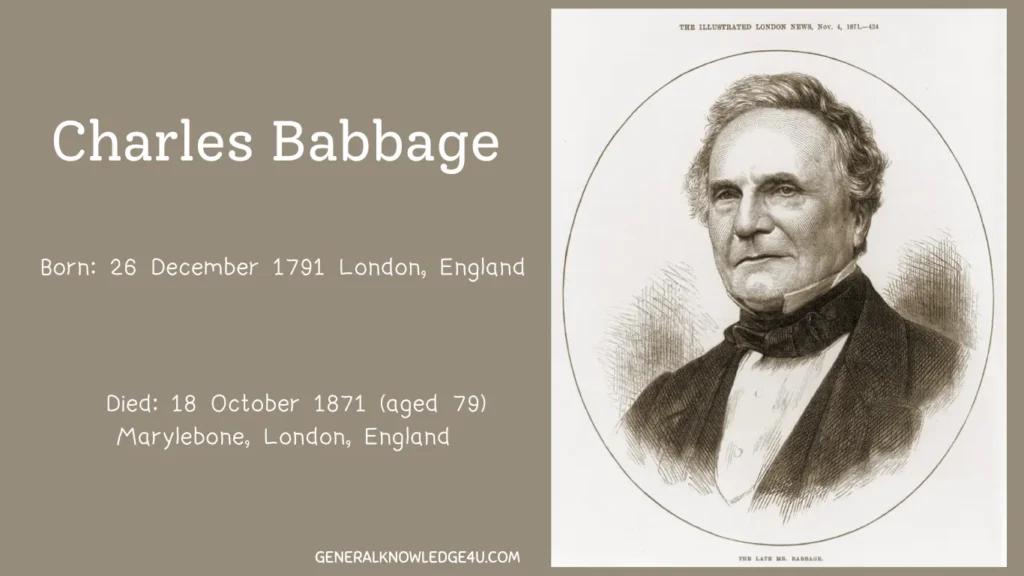
Q26. Who is considered the father of computers?
A. Charles Babbage is known as the father of computers for designing the Analytical Engine, which is considered the first general-purpose computing device.
Q27. What was ENIAC?
A. ENIAC (Electronic Numerical Integrator and Computer) was the first electronic general-purpose computer, completed in 1946, weighing 30 tons and occupying 1800 square feet.
Q28. Who invented the transistor?
A. The transistor was invented in 1947 by John Bardeen, Leon Cooper, and Robert Schrieffer at Bell Labs, revolutionizing computer design by replacing large vacuum tubes.
Q29. What is the first generation of computers (1940-1956)?
A. First generation computers used vacuum tubes for circuits. Key features: large size, high power consumption, heat generation, and limited speed. Example: ENIAC.
Q30. What characterized the second generation (1956-1963)?
A. Second generation computers used transistors, resulting in smaller size, faster processing, lower power consumption, and improved reliability compared to vacuum tubes.
Q31. What was the third generation (1964-1971)?
A. Third generation introduced Integrated Circuits (ICs), combining thousands of transistors on a single chip, enabling even more compact and powerful computers.
Q32. What defined the fourth generation (1971-present)?
A. Fourth generation featured microprocessors, combining entire CPU on a single chip. This enabled personal computers, reducing size and cost dramatically.
Q33. What is the fifth generation of computers?
A. Fifth generation (present and future) uses Artificial Intelligence, quantum computing, and neuromorphic computing. These computers aim to simulate human-like intelligence and reasoning.
Q34. What is the Intel 4004?
A. The Intel 4004, released in 1971, was the first commercial microprocessor with 2,300 transistors, operating at 108 kHz and marking the beginning of the microprocessor era.
Q35. What is Moore’s Law?
A. Moore’s Law, proposed by Gordon Moore in 1965, states that the number of transistors on a microchip doubles approximately every two years, resulting in exponential growth in computing power.
Q36. Who invented the personal computer?
A. Steve Jobs and Steve Wozniak created the first Apple Computer (1976), while IBM introduced the IBM PC (1981), making computers accessible to the general public.
Q37. What was the significance of the graphical user interface (GUI)?
A. GUI, pioneered by Xerox Alto (1973) and popularized by Apple Macintosh (1984), replaced command-line interfaces with visual icons, making computers user-friendly.
Q38. When was the World Wide Web invented?
A. Tim Berners-Lee invented the World Wide Web (WWW) in 1989 while working at CERN, creating HTML and the first web browser, revolutionizing global communication.

By M. Weik – https://ftp.arl.army.mil/ftp/historic-computers/ ; Transferred from pl.wikipedia to Commons by Masur using CommonsHelper., Public Domain, Link
Q39. What marked the beginning of cloud computing?
A. Cloud computing emerged in the 2000s with services like Amazon Web Services (AWS) in 2006, enabling on-demand access to computing resources over the internet.
Q40. What is the current state of quantum computing?
A. Quantum computers (2020s) harness quantum mechanics principles, offering exponential speed advantages for specific problems like cryptography and drug discovery, though still in early stages.
Q41. What is neuromorphic computing?
A. Neuromorphic computing involves designing computer chips that mimic the brain’s neural structures and processing methods, offering superior energy efficiency for AI tasks.
Q42. How has computing evolved regarding size and power?
A. From room-sized computers weighing tons (1950s) to portable laptops (1980s), smartphones (2000s), and now toward ubiquitous edge computing and wearables.
Q43. What role did the internet play in computing evolution?
A. The internet transformed computing from isolated systems to interconnected networks, enabling global communication, cloud computing, IoT, and collaborative digital ecosystems.
Q44. What is the significance of open-source software in computer history?
A. Open-source software (Linux, Apache, Firefox) democratized technology by allowing developers worldwide to contribute, innovate, and create freely, fundamentally changing the software industry.
Q45. How have storage capacities evolved?
A. From kilobytes (1970s) to megabytes (1980s), gigabytes (1990s), terabytes (2000s), and petabytes (2010s-2020s), enabling massive data processing and analytics capabilities.
Network & Internet Technology
Q46. What does HTTP stand for?
A. HTTP (HyperText Transfer Protocol) is the fundamental protocol of the World Wide Web, used for transmitting hypertext documents between browsers and web servers.
Q47. What is the difference between HTTP and HTTPS?
A. HTTP transmits data in plain text, making it vulnerable. HTTPS (HTTP Secure) encrypts data using SSL/TLS protocols, protecting against eavesdropping and tampering.
Q48. What is SSL/TLS?
A. SSL (Secure Sockets Layer) and TLS (Transport Layer Security) are cryptographic protocols that establish secure encrypted connections between clients and servers, protecting data in transit.
Q49. What is an IP Address?
A. An IP (Internet Protocol) Address is a unique numerical label assigned to each device on a network. IPv4 uses 32-bit addresses (example: 192.168.1.1), while IPv6 uses 128-bit addresses.
Q50. Explain DNS (Domain Name System).
A. DNS translates human-readable domain names (example: google.com) into IP addresses, enabling browsers to locate web servers on the internet.
Q51. What is a firewall?
A. A firewall is a security system that monitors and controls incoming and outgoing network traffic, blocking unauthorized access and malicious data based on predetermined rules.
Q52. Define VPN (Virtual Private Network).
A. A VPN creates an encrypted tunnel through the internet, allowing users to securely browse and communicate privately by masking their IP address and location.
Q53. What is bandwidth?
A. Bandwidth is the maximum amount of data that can be transmitted over a network connection per unit time, typically measured in megabits per second (Mbps) or gigabits per second (Gbps).
Q54. What is latency in networks?
A. Latency is the time delay between sending a request and receiving a response, measured in milliseconds (ms). Lower latency indicates faster response times.
Q55. Explain the OSI Model layers.
A. The seven layers are: Physical (cables), Data Link (switches), Network (routers, IP), Transport (TCP/UDP), Session, Presentation, and Application (HTTP, email). Each layer serves a specific function.
Q56. What is TCP/IP?
A. TCP/IP (Transmission Control Protocol/Internet Protocol) is the fundamental suite of protocols enabling data transmission across networks and the internet, ensuring reliable delivery.
Q57. What is the difference between UDP and TCP?
A. TCP is connection-oriented, ensuring reliable, ordered delivery with error checking. UDP is connectionless, faster but not guaranteed, used for real-time applications like video streaming.
Q58. What is a MAC address?
A. A MAC (Media Access Control) address is a unique hardware identifier assigned to network interface cards, used for local network communication within LANs.
Q59. Explain bandwidth throttling.
A. Bandwidth throttling is the deliberate limitation of internet speed by ISPs or network administrators, either to manage network congestion or control usage patterns.
Q60. What is mesh networking?
A. Mesh networking is a network topology where devices (nodes) relay data through multiple paths, improving coverage, reliability, and resilience compared to traditional networks.
Q61. What is PoE (Power over Ethernet)?
A. PoE allows network cables to deliver both data and electrical power to devices, simplifying installation of IP cameras, wireless access points, and other networked devices.
Q62. Define QoS (Quality of Service) in networking.
A. QoS is a set of techniques and technologies that prioritize network traffic based on application type, ensuring critical applications like video conferencing receive bandwidth priority.
Q63. What is SDN (Software-Defined Networking)?
A. SDN separates network control from forwarding functions, using software to manage network traffic flow, offering greater flexibility, scalability, and programmability than traditional networks.
Q64. What is 5G technology?
A. 5G (Fifth Generation) wireless technology offers speeds up to 100 Gbps, ultra-low latency (1ms), and high device density, enabling IoT, autonomous vehicles, and real-time applications.
Q65. Explain the difference between WAN and LAN.
A. LAN (Local Area Network) covers limited geographic areas (office, home) with high speeds. WAN (Wide Area Network) spans large distances, connecting multiple LANs with lower speeds.
Cybersecurity & Data Protection
Q66. What is malware?
A. Malware (malicious software) includes viruses, trojans, ransomware, spyware, and worms designed to damage computers, steal data, or compromise system security.
Q67. What is a virus vs. a worm?
A. A virus requires human action to spread (opening files), while a worm propagates independently across networks without user intervention.
Q68. What is ransomware?
A. Ransomware is malware that encrypts user data and demands payment for decryption. It can shut down operations and cause significant financial and reputational damage.
Q69. What is phishing?
A. Phishing is a social engineering attack where attackers impersonate trusted entities through emails or messages to trick users into revealing credentials or sensitive information.
Q70. Define a firewall.
A. A firewall is a security system that filters network traffic based on predetermined rules, blocking unauthorized access while allowing legitimate communications.

By Carlos Jones/ORNL – flickr, CC BY 2.0, Link
Q71. What is encryption?
A. Encryption converts readable data (plaintext) into unreadable format (ciphertext) using algorithms and keys, ensuring only authorized parties with decryption keys can access it.
Q72. Explain symmetric vs. asymmetric encryption.
A. Symmetric encryption uses one key for both encryption and decryption. Asymmetric uses a public key for encryption and private key for decryption, enabling secure key exchange.
Q73. What is a zero-day vulnerability?
A. A zero-day is a security flaw unknown to software vendors, exploited by attackers before developers can create patches, making it extremely dangerous.
Q74. What is multi-factor authentication (MFA)?
A. MFA requires multiple verification methods (password, SMS code, biometric) to access accounts, significantly reducing unauthorized access risk even if passwords are compromised.
Q75. What is a DDoS attack?
A. DDoS (Distributed Denial of Service) floods servers with traffic from multiple sources, overwhelming them and preventing legitimate users from accessing services.
Q76. Explain penetration testing.
A. Penetration testing involves authorized security professionals attempting to breach systems to identify vulnerabilities, helping organizations improve their security posture.
Q77. What is SIEM?
A. SIEM (Security Information and Event Management) systems collect and analyze security logs from multiple sources, detecting threats and enabling rapid incident response.
Q78. Define the principle of least privilege.
A. The principle of least privilege grants users only the minimum access rights necessary to perform their job, reducing the potential damage from compromised accounts.
Q79. What is a backdoor?
A. A backdoor is a hidden entry point into a system, intentionally or unintentionally created, allowing unauthorized users to bypass security measures and gain access.
Q80. Explain blockchain in cybersecurity.
A. Blockchain’s immutable, decentralized ledger technology enhances security through tamper-proof records, secure transactions, and transparent auditability for sensitive data.
Q81. What is biometric authentication?
A. Biometric authentication uses unique physical characteristics (fingerprints, facial recognition, iris scanning) for secure user verification, difficult to forge.
Q82. What is data classification?
A. Data classification categorizes information by sensitivity (public, confidential, secret), determining appropriate security controls and access restrictions for each level.
Q83. Define incident response.
A. Incident response is a structured process for detecting, investigating, containing, and recovering from security incidents to minimize damage and restore normal operations.
Q84. What is the CIA triad?
A. The CIA triad represents three pillars of information security: Confidentiality (data privacy), Integrity (accuracy), and Availability (accessibility) of information.
Q85. Explain zero trust security.
A. Zero trust assumes no implicit trust, requiring verification for every access attempt regardless of network location, significantly improving security against insider threats and breaches.
Cloud Computing & Edge Computing
Q86. What is cloud computing?
A. Cloud computing provides on-demand access to computing resources (servers, storage, software) over the internet, eliminating the need for on-premise infrastructure.
Q87. Explain SaaS, PaaS, and IaaS.
A. SaaS (Software as a Service) offers software applications online. PaaS (Platform as a Service) provides development platforms. IaaS (Infrastructure as a Service) offers computing resources.
Q88. What are the major cloud providers?
A. Major cloud providers include Amazon Web Services (AWS), Microsoft Azure, Google Cloud Platform (GCP), IBM Cloud, and Oracle Cloud.
Q89. What is auto-scaling in cloud computing?
A. Auto-scaling automatically adjusts computing resources based on demand, adding capacity during peak usage and reducing during low usage to optimize costs.
Q90. Define cloud migration.
A. Cloud migration is transferring applications, data, and workloads from on-premise infrastructure to cloud platforms, requiring careful planning and execution.
Q91. What is edge computing?
A. Edge computing processes data locally on devices or edge servers near data sources rather than sending all data to central cloud servers, reducing latency and bandwidth usage.
Q92. How does edge computing differ from cloud computing?
A. Cloud computing centralizes processing in data centers. Edge computing distributes processing to network edges closer to data sources, enabling real-time processing.
Q93. What are IoT and its relationship with edge computing?
A. IoT (Internet of Things) connects billions of physical devices. Edge computing enables these devices to process data locally, reducing cloud server burden and improving response times.
Q94. What is a CDN (Content Delivery Network)?
A. A CDN is a network of distributed servers globally positioned to deliver content to users from the closest server location, improving speed and reducing latency.
Q95. Explain serverless computing.
A. Serverless computing abstracts infrastructure management; developers write code executed on cloud platforms without managing servers, paying only for actual execution time.
Q96. What is containerization in cloud?
A. Containerization packages applications with dependencies into lightweight containers (Docker), enabling consistent deployment across different environments.
Q97. Define microservices architecture.
A. Microservices break applications into small, independent services that communicate through APIs, enabling scalability, flexibility, and independent deployment.
Q98. What is API management?
A. API management platforms govern APIs throughout their lifecycle, including creation, security, versioning, monitoring, and retirement, enabling controlled integration.
Q99. What are the benefits of cloud computing?
A. Benefits include scalability, cost efficiency, global accessibility, automatic updates, disaster recovery, and reduced IT infrastructure burden.
Q100. What are cloud security concerns?
A. Major concerns include data breaches, compliance violations, insecure APIs, account hijacking, and loss of control over data stored on third-party servers.
Artificial Intelligence & Machine Learning
Q101. What is artificial intelligence (AI)?
A. AI refers to computer systems designed to perform tasks requiring human-like intelligence, including learning from data, recognizing patterns, and making decisions.
Q102. What is the difference between AI, ML, and deep learning?
A. AI is the broader field. Machine Learning (ML) is a subset enabling computers to learn from data. Deep Learning uses neural networks with multiple layers.
Q103. What are supervised and unsupervised learning?
A. Supervised learning uses labeled training data with known outcomes. Unsupervised learning finds patterns in unlabeled data without predefined answers.
Q104. Define neural networks.
A. Neural networks are computing systems inspired by biological neurons, consisting of interconnected nodes organized in layers that learn to recognize patterns in data.
Q105. What is natural language processing (NLP)?
A. NLP enables computers to understand and process human language, powering applications like chatbots, translation services, and sentiment analysis.
Q106. What is computer vision?
A. Computer vision enables machines to interpret and understand visual information from images and videos, used in facial recognition and autonomous vehicles.
Q107. Explain reinforcement learning.
A. Reinforcement learning trains models through trial and error, receiving rewards for correct actions and penalties for incorrect ones, optimizing decision-making over time.
Q108. What are generative AI models?
A. Generative AI creates new content (text, images, code) by learning patterns from training data, exemplified by GPT models and DALL-E.
Q109. What is transfer learning?
A. Transfer learning reuses pre-trained models on new tasks, reducing training time and data requirements by leveraging knowledge learned on previous problems.
Q110. Define overfitting in machine learning.
A. Overfitting occurs when models learn specific training data too well, including noise, resulting in poor performance on new unseen data.
Q111. What is feature engineering?
A. Feature engineering selects, transforms, or creates relevant features from raw data to improve model performance and accuracy in predictions.
Q112. Explain clustering in machine learning.
A. Clustering groups similar data points into clusters without predefined labels, useful for customer segmentation, anomaly detection, and pattern discovery.
Q113. What are decision trees?
A. Decision trees are models using tree-like structures to make predictions by recursively splitting data based on feature values, interpretable and effective.
Q114. What is the random forest algorithm?
A. Random Forest combines multiple decision trees, each trained on different data subsets, improving prediction accuracy and reducing overfitting.
Q115. What are the ethical considerations in AI?
A. Ethical concerns include bias in training data, privacy violations, job displacement, algorithmic transparency, and responsible AI development ensuring fairness.
Web3, Blockchain & Cryptocurrency
Q116. What is blockchain technology?
A. Blockchain is a decentralized, immutable ledger technology where data is organized in blocks linked cryptographically, ensuring transparency and security.
Q117. What is Bitcoin?
A. Bitcoin is the first cryptocurrency created in 2009 by Satoshi Nakamoto, using blockchain technology to enable peer-to-peer transactions without central intermediaries.
Q118. What is Ethereum?
A. Ethereum is a blockchain platform enabling smart contracts and decentralized applications (dApps), expanding blockchain use beyond financial transactions.
Q119. What are smart contracts?
A. Smart contracts are self-executing programs on blockchain that automatically execute agreed-upon conditions without intermediaries, transparent and tamper-proof.
Q120. What is Web3?
A. Web3 represents a decentralized internet vision using blockchain, enabling users to control their data, cryptocurrencies, and digital assets without centralized platforms.
Q121. What are NFTs (Non-Fungible Tokens)?
A. NFTs are unique digital assets on blockchain representing ownership of specific items (art, collectibles), each with distinct properties and verified ownership history.
Q122. What is DeFi (Decentralized Finance)?
A. DeFi uses blockchain and smart contracts to replicate traditional financial services (lending, borrowing, trading) without banks, enabling peer-to-peer finance.
Q123. Explain mining in cryptocurrency.
A. Mining involves solving complex cryptographic problems to validate transactions and create new cryptocurrency blocks, securing the network and rewarding miners.
Q124. What is a cryptocurrency wallet?
A. A cryptocurrency wallet stores private keys enabling users to send and receive cryptocurrencies, analogous to traditional bank accounts but decentralized.
Q125. What are stablecoins?
A. Stablecoins are cryptocurrencies designed to maintain stable value by backing to fiat currencies (USD) or commodities, reducing volatility compared to other cryptocurrencies.
DevOps, Docker & Kubernetes
Q126. What is DevOps?
A. DevOps combines software development and IT operations, emphasizing automation, continuous integration/deployment, monitoring, and collaboration for faster, reliable software delivery.
Q127. What is Docker?
A. Docker is containerization software that packages applications with dependencies into lightweight containers, ensuring consistency across development, testing, and production environments.
Q128. What is a container?
A. A container is a lightweight, standalone executable package containing applications and all dependencies (libraries, runtime), running identically across different systems.
Q129. What is Kubernetes?
A. Kubernetes is an open-source container orchestration platform that automates deployment, scaling, and management of containerized applications across clusters.
Q130. Explain CI/CD (Continuous Integration/Continuous Deployment).
A. CI automates code integration and testing. CD automates deployment to production, enabling frequent, reliable software releases with minimal manual intervention.
Q131. What is GitLab and GitHub?
A. Git-based platforms for version control, collaboration, and CI/CD pipeline management. GitHub is GitHub-owned while GitLab offers self-hosted alternatives.
Q132. What is infrastructure as code (IaC)?
A. IaC uses code to define and provision infrastructure, enabling version control, consistency, and automation of infrastructure deployment and updates.
Q133. What is microservices architecture?
A. Microservices break applications into independent, loosely coupled services communicating via APIs, enabling scalability, flexibility, and independent deployment.
Q134. Explain load balancing.
A. Load balancing distributes network traffic across multiple servers, optimizing resource usage, improving reliability, and preventing server overload.
Q135. What is monitoring and observability in DevOps?
A. Monitoring tracks system metrics and alerts on anomalies. Observability provides deeper insights into system behavior through logs, metrics, and traces for debugging.
Data Science & Big Data
Q136. What is big data?
A. Big data refers to extremely large datasets (volume), diverse types (variety), and high generation speed (velocity) that traditional tools struggle to process efficiently.
Q137. What are the 4 V’s of big data?
A. Volume (quantity), Velocity (speed), Variety (types), and Veracity (accuracy/quality) characterize big data, requiring advanced technologies for processing and analysis.
Q138. What is data mining?
A. Data mining discovers patterns, correlations, and insights from large datasets using statistical and machine learning techniques, extracting valuable business intelligence.
Q139. What is ETL (Extract, Transform, Load)?
A. ETL processes extract data from sources, transform it into usable formats, and load into data warehouses or lakes for analysis and storage.
Q140. What is a data warehouse?
A. A data warehouse is a centralized repository storing structured historical data from multiple sources, optimized for analysis and business intelligence.
Q141. What is a data lake?
A. A data lake is a large repository storing raw data in various formats, enabling flexible analysis without predefined schemas, useful for big data exploration.
Q142. What is data visualization?
A. Data visualization presents data graphically through charts, graphs, and dashboards, making complex information understandable and enabling better decision-making.
Q143. What is predictive analytics?
A. Predictive analytics uses historical data and machine learning to forecast future events, trends, and behaviors, guiding proactive business decisions.
Q144. Explain sentiment analysis.
A. Sentiment analysis uses NLP to determine emotional tone from text data, extracting positive, negative, or neutral sentiment from customer feedback and social media.
Q145. What are data scientist skills?
A. Essential skills include statistics, machine learning, programming (Python, R), SQL, data visualization, domain knowledge, and communication abilities.
Programming Languages & Software Development
Q146. What are the main programming paradigms?
A. Main paradigms include procedural (C, Pascal), object-oriented (Java, C++), functional (Lisp, Haskell), and declarative (SQL, HTML) programming approaches.
Q147. What is Python and its applications?
A. Python is a versatile, readable language used for web development, data science, machine learning, automation, and scripting, known for extensive libraries.
Q148. What is Java and why is it popular?
A. Java is platform-independent, runs on JVM (Java Virtual Machine), and is widely used in enterprise applications, Android development, and large-scale systems.
Q149. What are the SOLID principles?
A. SOLID represents principles for better code design: Single Responsibility, Open/Closed, Liskov Substitution, Interface Segregation, and Dependency Inversion.
Q150. What is agile software development?
A. Agile methodology emphasizes iterative development, customer collaboration, continuous feedback, and adaptive planning, enabling faster delivery of quality software.
Emerging Technologies & Future Trends
Q151. What is quantum computing’s potential?
A. Quantum computers process information exponentially faster than classical computers for specific problems, with applications in cryptography, drug discovery, and optimization.
Q152. How is AI transforming cybersecurity?
A. AI enhances cybersecurity through automated threat detection, behavior analysis, predictive threat hunting, and rapid incident response, defending against sophisticated attacks.
Q153. What is the significance of 5G beyond faster internet?
A. 5G enables ultra-low latency, massive device connectivity, and edge computing capabilities, powering autonomous vehicles, IoT, smart cities, and real-time applications.
Q154. What are the sustainability implications of computing?
A. Computing contributes significantly to carbon emissions. Green computing focuses on energy efficiency, renewable energy usage, and reduced electronic waste.
Q155. What is the future of work in tech?
A. Future work emphasizes remote/hybrid models, AI augmenting human capabilities, continuous learning, cybersecurity skills, and ethical AI development expertise.
Conclusion
The ability to use computers effectively has gone from being a “nice-to-have” skill to an absolute must in today’s digital world. The 150 questions and answers in this guide will give you the basic knowledge and cutting-edge insights you need to do well in any situation, whether you’re working in a business, trying to do well in school, or getting ready for a lucrative tech job.
Q1. Is this guide suitable for complete beginners?”
Absolutely! This guide is designed for learners at all levels with explanations starting from fundamentals.
Q2. Will this guide help me prepare for competitive exams?
Yes, this guide covers topics commonly tested in UPSC, Banking, SSC and other competitive exams.
Q3. Can this guide help in technical job interviews?
Definitely! This guide serves as excellent interview preparation for various IT roles.











Leave a Comment